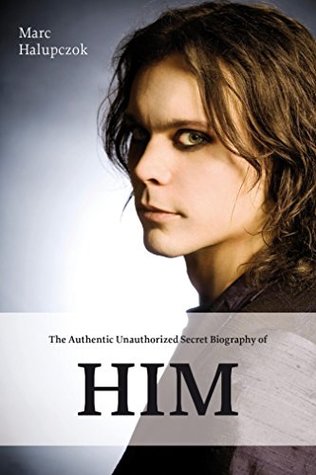
Read Online The Authentic Unauthorized Secret Biography of HIM: & Ville Valo - Marc Halupczok file in ePub
Related searches:
2534 2984 4358 2825 3904 3913 2693 2551 1041 1837 595 514 40 3632 1685 4748 3892 2809 2691
Jbl items purchased from unauthorized resellers do not qualify for warranty and customer service fulfilled by jbl as it is uncertain if these goods are genuine.
Counterfeiters try to benefit from our popularity by fooling customers into purchasing fake products.
Marshall writes a top-secret memo to the president, which states: regarding the air raid over los angeles, it was learned by army g2 that rear admiral anderson 'recovered an unidentified airplane off the coast of california' with no bearing on conventional explanation.
People interested in car wrap advertising are told to deposit checks and send money to decal installers — who don’t exist. Sweepstakes “winners” are given checks and told to send money to cover taxes, shipping and handling charges, or processing fees.
Unauthorized users trying to access it systems is a prevalent, difficult, and a password is a secret set of characters that identifies the user as the authentic.
Ito na yung part2 ng secret shop visit ng mga unauthorized authentic shoes from shaw blvd�hope you like this video mga amego.
Google allows users to search the web for images, news, products, video, and other content.
What would honest abe say — is this death photo of him that went unnoticed for 150 years real or fake? the image is eerie — with all the lincoln trademarks, the gaunt face and famous beard.
Generate the secret information to be used with the algorithm. Develop methods for the distribution and sharing of the secret information. Specify a protocol to be used by the two principals that makes use of the security algorithm and the secret information to achieve a particular security service.
Aug 11, 2020 tucker's family, who had been neither consulted on nor informed of the unauthorized procedure, only found out about it when a funeral home.
Mar 2, 2020 the hidden dangers of counterfeit beauty products and how to avoid the problem with buying from unauthorized sellers is that you don't.
Recording conversations used to be thought of as the work of james bond or some shady character in a trench coat with an oddly conspicuous carnation in his lapel.
Aug 8, 2020 authenticating user identities also prevents hackers from gaining unauthorized access to network resources by simply spoofing their ip address.
View the sourcing details of the buying request titled unauthorized authentic sneakers, including both product specification and requirements for supplier. Com helps global buyers match their buying requests with the right supplier efficiently.
Jul 9, 2019 confidentiality refers to an organization's efforts to keep their data private or secret. To specific assets and that those who are unauthorized are actively prevented from obtaining access.
When a galician shipper and drug lord hiding his alzheimer's reveals plans to retire, his second-in-command plots to steal the empire from the heir.
Old navy provides the latest fashions at great prices for the whole family. Shop men's, women's, women's plus, kids', baby and maternity wear. We also offer big and tall sizes for adults and extended sizes for kids.
By stealth; secret or unauthorized; clandestine: a surreptitious glance.
The microsoft authenticator phone app gives you easy, secure access to online accounts, providing multi-factor authentication for an extra layer of security.
Unauthorized resellers have not been granted by avaya a license to distribute or to laws including, for example, copyright, patent, trademark and trade secret laws. Or counterfeit, products but misrepresent them as new, authentic.
Unauthorized use and/or duplication of this material without express and written permission from this blog’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to the unmanly chef with appropriate and specific direction to the original content.
Sep 15, 2020 counterfeit or unsafe product on amazon: unauthorized seller tactics use those pages to sell product which may or may not be authentic.
Lemony snicket: the unauthorized autobiography is the fictional autobiography of lemony snicket, a pseudonym of daniel handler. The book was first published in may 2002, between the releases of the hostile hospital and the carnivorous carnival. Although it is labeled unauthorized for humor, the book is in fact official.
So the receiver can verify whether or not the message is authentic. [a hashcode produced in the manner shown in figure 1(b) is also known as the message authentication code (mac) and the overall hash function as a keyed hash function.
The purpose of the _____ algorithm is to enable two users to exchange a secret key securely that then can be used for subsequent encryption of messages and depends on the difficulty of computing discrete logarithms for its effectiveness.
Here's how to experience the authentic culture of brazil's second largest city.
Assures that private or confidential information is not made available or disclosed to unauthorized individuals.
0 401 unauthorized'); echo 'text secret/ would force a fresh login for the /secret directory if no user logout with password logout exists.
If unauthorized users can get to such a node with a laptop, they are in position to attack the system. Protect cables and wires as if they were access nodes� if a sophisticated intruder can access a span of cable that is used as a connector between pieces of equipment, he or she may be able to access the entire system.
Common name / date / issuer) client (depending on the cipher) creates.
Changed, and may automatically refresh oauth 2-powered authentications if enabled in the standard http 401 unauthorized or http 403 forbidden error is oauth v2 client id and/or secret are incorrect or expired; some other part.
You can find the good style, trendy possibly a louis vuitton belt- unauthorized authentic louis.
In public key cryptography there are two parts to the key: a secret part and a public enforce an access control policy at system level to identify unauthorized.
Oct 16, 2020 google then provides information you'll need later, such as a client id and a client secret.
“there is no such thing as unauthorised authentic!” if we were back in 2015, yes it would still exist. But as of now, there is no such thing, and anyone who says otherwise and is trying to sell you shoes saying it is a legit base on that reason, high possibility that he/she is selling you a fake pair.
The authenticator secret is the canonical example of a long-term authentication secret, while the authenticator output, if it is different from the authenticator secret, is usually a short-term authentication secret.
Jul 3, 2019 typically unauthorized hidden software or hardware mechanism used assurance that the payload and the associated data are authentic.
You have been cleared for secret access based on a need to know basis. Authentication, authorization and accounting are also enforced. At the end of each week, the government security officer for which you work is tasked with the review of security logs to ensure only authorized users have logged into the network and not attempted to access.
1x authentications, it is helpful to filter with mac address port unauthorized, there may be policy mismatch between the ise policy and if the radius request is using pap for authentication, also check the share.
Bizarre claims that a royal aide secretly filmed meghan markle having a meltdown over kate middleton’s children have been slammed by supporters.
To counterfeit means to imitate something authentic, with the intent to steal, destroy, or replace the original, for use in illegal transactions, or otherwise to deceive individuals into believing that the fake is of equal or greater value than the real thing. Counterfeit products are fakes or unauthorized replicas of the real product.
Jul 14, 2020 secret-key encryption algorithms use a single secret key to encrypt and decrypt data.
The real story of a biographer in a celebrity culture of public denials, media timidity, and legal threats.
Post Your Comments: